
How to use KMS and IAM to enable independent security controls for encrypted data in S3 | AWS Security Blog

How can I log into my Amazon EC2 instance if I receive an error that the server refused our key? - Hosting Journalist.com

amazon ec2 - "Server Refused our key" after launching instance from private EBS AMI - Stack Overflow
AWS ec2 instance no supported authentication methods available server sent publickey gssapi-keyex gssapi-with-mic | Edureka Community











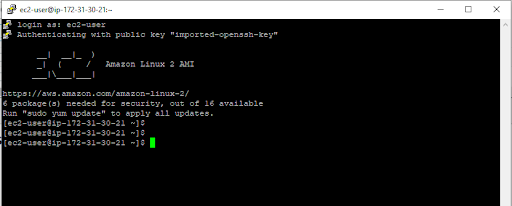




![Server Refused Our Key" Error [Solved] Server Refused Our Key" Error [Solved]](https://ws-na.amazon-adsystem.com/widgets/q?_encoding=UTF8&ASIN=B01AWH05GE&Format=_SL250_&ID=AsinImage&MarketPlace=US&ServiceVersion=20070822&WS=1&tag=dee22-20&language=en_US)
